Small Biz Hacker Protection
 Small Biz Hacker Protection: a reader asks…
Small Biz Hacker Protection: a reader asks…
I have a small business and am getting worried about getting hacked. Not my website, my on-premises infrastructure. Everywhere I read about how hackers are starting to target people like me. I don’t have a lot of IT infrastructure, just a few computers, a file server and some laptops that my sales team uses all over the territory. Do you have a short and sweet hit list of things I should do/don’t?
Short and sweet? How about a dirty dozen. I wish I could cut it down to three, but the threats are just too varied to allow for a simple protection plan. Without all the background, here’s the hit-list (in no particular order):
- If you’re managing your own email, activate your servers’s “Sender Policy Framework” and if your email is outsourced, make sure your service provider does this.
- Use your File Server for file sharing, skip the “sneakernet”. If you have to use thumbdrives, make sure they are 100% safe. Hackers like to sprinkle these in parking lots and sidewalks. While your’e at it, avoid non-commercial CDs, they too can have malware hidden on them.
 Use good, strong (meaning long), and unique passwords. Make sure your employees are doing likewise (of course, a Password Manager like LastPass is required to meet the requirement for unique-ness).
Use good, strong (meaning long), and unique passwords. Make sure your employees are doing likewise (of course, a Password Manager like LastPass is required to meet the requirement for unique-ness).- Don’t let your employees use public, open, or even customer’s Wi-Fi when on the road. You can get a Mi-Fi device for each of them with a low-cost data-sharing plan.
 Keep all operating systems and installed software and apps up-to-date. Be scrupulous about this, outdated or unpatched software is the easiest way for hackers to gain entry.
Keep all operating systems and installed software and apps up-to-date. Be scrupulous about this, outdated or unpatched software is the easiest way for hackers to gain entry.- Be diligent in backing up everything.
- Train your employees to be wary internet & computer users. Automatic clicking often opens up a can of hacker worms.
- Get someone (an IT professional, not your uncle or an employee’s son) to periodically look at your your system from a security standpoing. Penetration testing is a fabulous idea!
- Make sure you have good networking equipment. Old equipment may be more vulnerable. Also keep the firmware updated, and make sure your security settings are strong. For that matter, old, outdated computers are also a security risk.
- Eyes open in your space. Question any stranger who gains or wants to gain entry to your business. That’s both physical and virtual.
 Don’t trust email, it’s notorious for fake-ness because it’s never been a verified-identity communications platform. Anybody can send you email and make it look like it came from someone you know and trust.
Don’t trust email, it’s notorious for fake-ness because it’s never been a verified-identity communications platform. Anybody can send you email and make it look like it came from someone you know and trust.- Make sure the other end of a virtual communication of any sort is real. It doesn’t hurt to pick up the phone and confirm that the website offering you supplies or services is a real business.
There, short and sweet. Feel free to use the comments section below if you need amplification on any of the items on the list. And I’m happy to take suggestions for other things to add to this list, if you have real-life experience and lessons learned to share, please share!
This website runs on a patronage model. If you find my answers of value, please consider supporting me by sending any dollar amount via:
or by mailing a check/cash to PosiTek.net LLC 1934 Old Gallows Road, Suite 350, Tysons Corner VA 22182. I am not a non-profit, but your support helps me to continue delivering advice and consumer technology support to the public. Thanks!
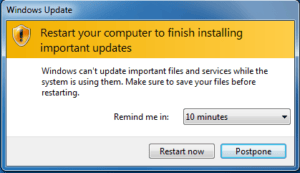 Keep all operating systems and installed software and apps up-to-date. Be scrupulous about this, outdated or unpatched software is the easiest way for hackers to gain entry.
Keep all operating systems and installed software and apps up-to-date. Be scrupulous about this, outdated or unpatched software is the easiest way for hackers to gain entry. Don’t trust email, it’s notorious for fake-ness because it’s never been a verified-identity communications platform. Anybody can send you email and make it look like it came from someone you know and trust.
Don’t trust email, it’s notorious for fake-ness because it’s never been a verified-identity communications platform. Anybody can send you email and make it look like it came from someone you know and trust.