The Weak Link of MFA

The Weak Link of MFA: a reader asks…
I’ve been taking your advice about setting up 2-factor authentication, also called Multi-factor authentication (MFA). I’ve done my email, banking and other financial accounts. I also did some of my shopping accounts, although not everyone has this feature. Question, are my MFA-secured accounts now safe from hackers?
Your accounts are much safer than they were when secured with just a username and password, but nothing is ever 100%. In the case of MFA, there are several weak links. The weakest is, unfortunately, you. Here’s a scenario:

You get an email from an online entity that includes a handy link to log into your account. You click that link. Your web browser opens a web page that looks identical to the real one. The login process is identical and handles your username, password, and MFA credentials the same as on the real site. However, the site you’re on is a clone of the real site and simply mirrors the login process. As you enter your username and password, it sends them to the real site and then mirrors the MFA code box back. You type in that MFA code, and it sends that to the real site. Viola, the hacker doing this now has access to your account on the real site.
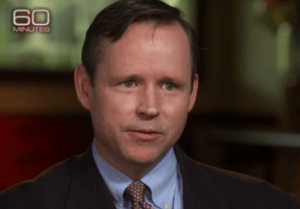
How do you stop this? Don’t click links in emails, text messages, social media posts, etc. They are hugely convenient, but an even huger security vulnerability. The hackers and scammers know that more people are using MFA, and have crafted these tools to circumvent your protection. One such toolkit is called Starkiller, and it is for sale on the dark web to anyone. You can get more details from one of my favorite security advisors, Brian Krebs. He writes about this at https://krebsonsecurity.com/2026/02/starkiller-phishing-service-proxies-real-login-pages-mfa/
The second weak link is the MFA method you choose. Some online organizations only offer the text message method: you log in with a username and password, and the website texts you a code to enter on the next screen. The weakness here is that text messages can be intercepted. The solution to this is to use an authentication app instead of text messaging wherever possible. This is a little more complicated to set up, but it offers better security. There are many authentication apps available, including Google Authenticator and Microsoft Authenticator, as well as authenticators embedded in or offered alongside popular password managers.

An improvement on this is the so-called “Passwordless Sign On” feature offered by a growing number of online organizations. In this case, you don’t even have a password, and you use the authentication app to approve your login. The upside is that there’s one less item to enter (your password). The downside is that some entities with this feature require you to use a specific authenticator (often their own brand). Apply this across your various accounts, and you may find yourself having to use several different authenticators. Ugh!
The third weak link is the ‘username’ – this is often your email address, and many entities that have a separate username still allow you to log in with your email address. Based on the amount of spam you get, your email address is almost certainly on a list for sale on the dark web, along with any compromised passwords you may have used in the past. Hackers buy these lists and try brute-force attacks on various online accounts. This is all automated; there’s no shady character typing in passwords. Hackers and scammers are increasingly using AI to make their attacks more sophisticated, making scams harder to discern.

This is not really something you can do anything about, other than to use a good password manager so that all your passwords are long, unguessable, and unique. I get that organizations want to make logging into their sites as easy as possible, and are balancing that ease with security, leaning more towards ease. If you don’t already have a password manager, there are many out there, including 1Password, Keeper, LastPass, Apple Password, NordPass, etc. I do not recommend you use the password manager built into your web browser (in particular, Chrome), as its security is only as strong as your account with that browser, and web browsers always have security vulnerabilities. That’s why the browser gets patched and updated so very often.
The fourth weak link is the online entities where you have accounts. Hackers are sneaking into their networks and grabbing credentials, personal information, and anything else of value. Worse, these entities are notorious for not telling you they’ve been hacked, sometimes for years. For this, your best bet is to keep an eye on all spending, credit cards, and bank accounts. Sign up for credit protection and freeze your credit. Watch for news about hacks, and take action to secure your accounts if a breach is reported. For shopping sites, don’t save your credit card; only enter it when making a purchase.
Whenever you’re online, you should be operating with a bit of paranoia, particularly when it comes to email, text messages, and social media. These are such easy vectors for attacks, and the hackers and spammers certainly use them. Many people see dozens of scam and hack attempts using these vectors on a daily basis. Vigilance and good internet hygiene are critical. Don’t click links in most anything; if you want to visit a website, type the URL into your web browser. It’s not as convenient, but much safer.
This website runs on a patronage model. If you find my answers of value, please consider supporting me by sending any dollar amount via:
or by mailing a check/cash to PosiTek.net LLC 1934 Old Gallows Road, Suite 350, Tysons Corner VA 22182. I am not a non-profit, but your support helps me to continue delivering advice and consumer technology support to the public. Thanks!